מאמרים מאת יוסי שביט
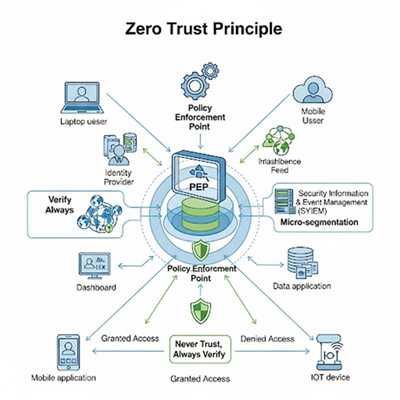
In cybersecurity for industrial control systems and OT networks, we increasingly recognize and assume that the attacker will find their way into the OT network, and therefore we must adopt a Zero Trust policy. In this article I published, I will explain how to implement this in industrial control systems, which represent the soft underbelly of cyberattacks in industrial plants https://online.fliphtml5.com/iawl/zift/?fireglass_rsn=true#p=44
קרא עודThis article seeks to examine a systemic issue that repeatedly arises during my site visits to industrial facilities: the lack of clear responsibility for cybersecurity within industrial control systems and OT networks. Yosi
קרא עודIn today’s interconnected industrial landscape, the boundaries between IT and OT environments have become increasingly blurred. Industrial Control Systems (ICS) and other Operational Technology (OT) environments, which once relied on physical isolation for security, are now deeply integrated with enterprise networks, cloud systems, and remote access capabilities. This integration brings operational efficiency but also unprecedented cyber risks. Yosi
קרא עודModern swimming pools, especially large public or industrial facilities, increasingly rely on Industrial Control Systems (ICS) to manage water treatment, disinfection, and chemical balancing. These systems often control hazardous materials such as hydrochloric acid and hypochlorite, or other toxin materials used for pH regulation. While automation improves efficiency and safety under normal conditions, it also introduces significant cybersecurity risks.
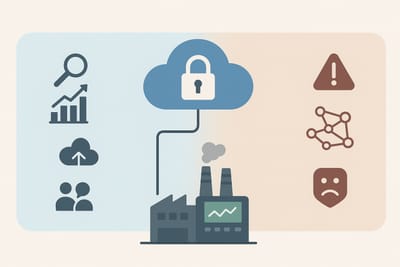
קרא עודDuring my visits to industrial plants that contain numerous industrial control systems and SCADA systems (ICS) operating within segmented and protected OT networks, the question often arises among plant personnel whether it is advisable to move data to the cloud or remain in an on-prem configuration. Since these industrial plants are designed to generate profit, I do not find it appropriate to restrict them or prevent cloud adoption solely for cybersecurity reasons. My approach is to enable the business and support cloud migration when it demonstrates profitability, but to do so with great caution, implementing appropriate security measures to address cybersecurity concerns and the exposure surfaces identified throughout the cloud-migration project.
קרא עודIntroduction Critical infrastructure relies on industrial control systems (ICS/OT) to ensure continuous, safe, and reliable operation. In recent years, there has been a sharp increase in cyberattacks targeting these systems, exploiting unique characteristics such as legacy components, vendor connectivity, and complex supply chains. Many mistakenly believe that improving cyber resilience in OT environments is similar to the process of strengthening resilience in IT environments. This perception stems primarily from a lack of sufficient understanding of the OT domain and an adherence to historically rooted IT-centric assumptions. In this article, I will examine the fundamental gap between cybersecurity concepts originating in the IT domain and the unique requirements of industrial control systems, and present a practical security approach based on processes, safety, and operational continuity, not solely on technology.
קרא עודIn recent years, we have witnessed a significant increase in both the volume and sophistication of cyberattacks targeting industrial facilities and critical infrastructure. Industrial Control Systems (ICS) and OT networks have become prime targets due to their potential to cause physical damage, disrupt production, and even endanger human life. One of the major challenges during a severe cyber incident is the need to rapidly transition from computer-controlled operations to manual operations when digital control of systems is compromised or completely lost. In this article I will examine the implications of such a transition, with a strong emphasis on safety aspects, risk management, and the protection of human life.
קרא עודModern power plants, whether fueled by natural gas, diesel' coal, nuclear energy, or renewable sources, rely on a combination of industrial processes, hazardous materials, and computerized control systems. These materials are essential for production but also pose serious health, safety, and environmental risks if mishandled or compromised. As industrial control systems (ICS) and Operational Technology (OT) become increasingly networked, so too does the attack surface for threat actors targeting critical infrastructure. This article explores key hazardous materials in power plants, their roles, how they integrate with operational control systems, and what cyber risks they introduce along with recommendations to protect them.
קרא עוד